Introduction
Researchers at the University of California, Santa Barbara have developed a new technique called Wiffract that can extract information from Wi-Fi signals reflected off walls. By analyzing the unique shape of the Wi-Fi reflections, the system is able to decode the shape of motionless objects on the other side of the wall.
Previous Methods
Previous methods of Wi-Fi snooping relied on detecting movement to understand the shape of people’s bodies as they moved through a room. However, the new technique does not require any movement and can accurately trace the shape of objects solely based on the reflection of Wi-Fi signals.
How it Works
When radio waves hit a sharp or tightly curved edge, they are diffracted into a specific shape known as a Keller cone. By measuring and mathematically tracing back this shape, the researchers can determine the location of the point that created it. With enough Keller cones, a 3D map of the edges of objects within a room can be created.
Experimental Setup
In their tests, the researchers used three off-the-shelf Wi-Fi transmitters to send signals into the room. They recorded the reflections using a tower of Wi-Fi receivers mounted on a remote-controlled car. By moving the car and the receivers back and forth, they were able to measure reflected signals as if they had a large 2D grid receiver.
Results
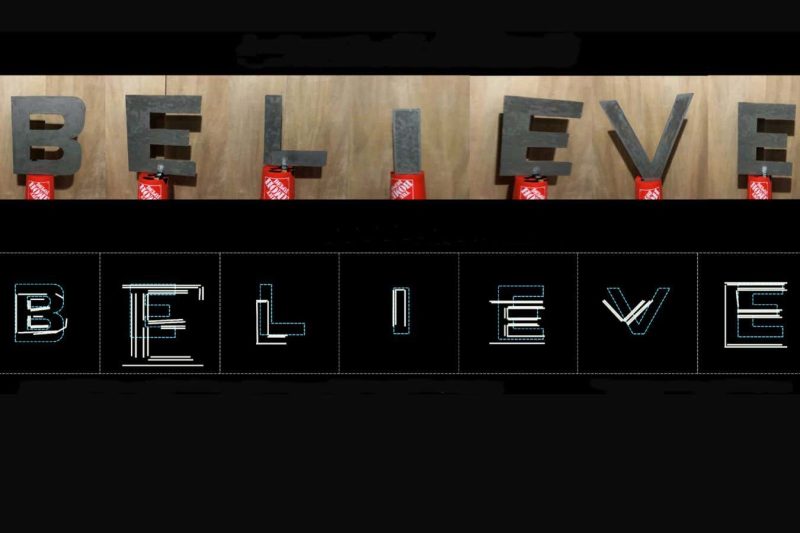
The researchers were able to create detailed images of the edges of objects in a room, even through a wall. They were also able to read the text of a 3D sign using this method. However, the amount of detail seen is reduced when thick walls are involved.
Potential Applications and Risks
This technique could have potential applications in smart homes and security systems. However, it also raises privacy concerns. As this technology develops further, it is important to have discussions about privacy and how to address potential risks.
Conclusion
Using Wi-Fi signals reflected off walls, researchers have developed a technique to extract information about motionless objects on the other side. This method has potential practical applications but also comes with privacy risks that need to be addressed.